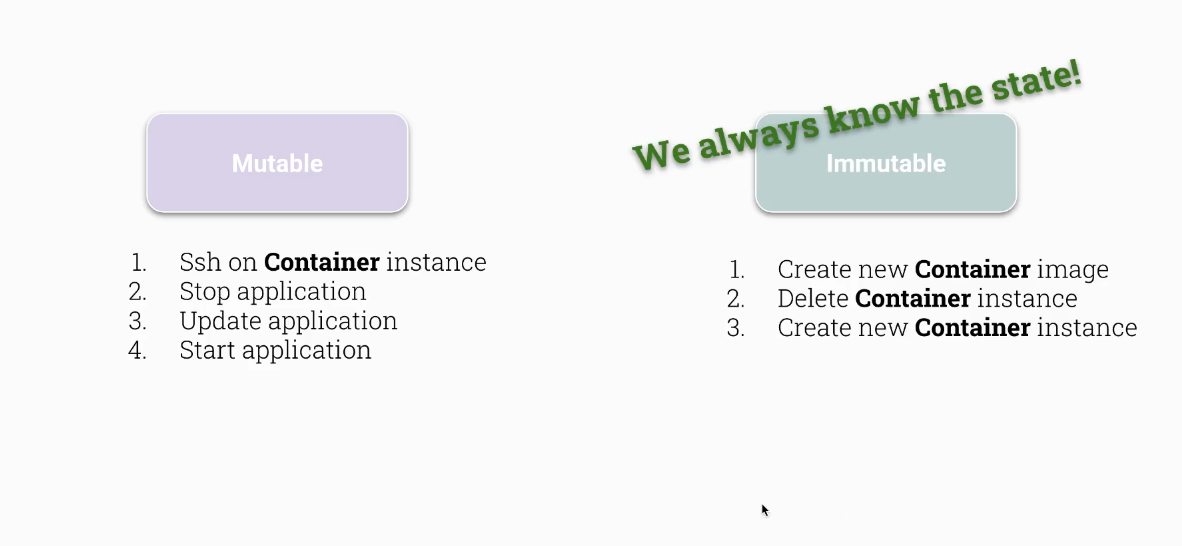
CKS Immutability of containers at runtime
How to enforce container immutability at runtime in Kubernetes using startupProbe, readOnlyRootFilesystem, and emptyDir volumes.
- advanced deployment methods
- easy rollback
- more reliability
- better security (on container level)
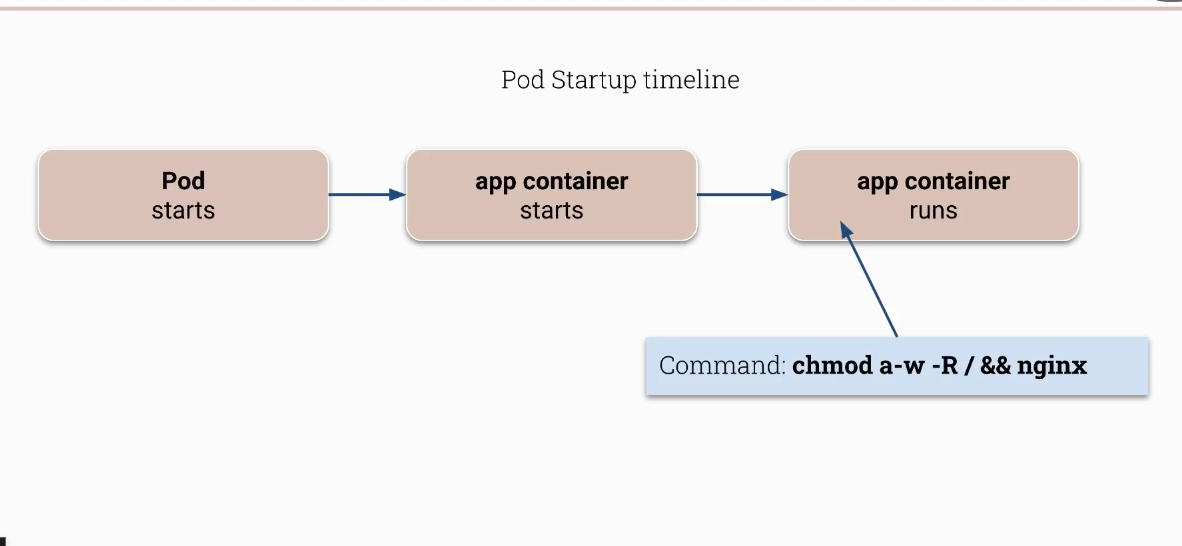
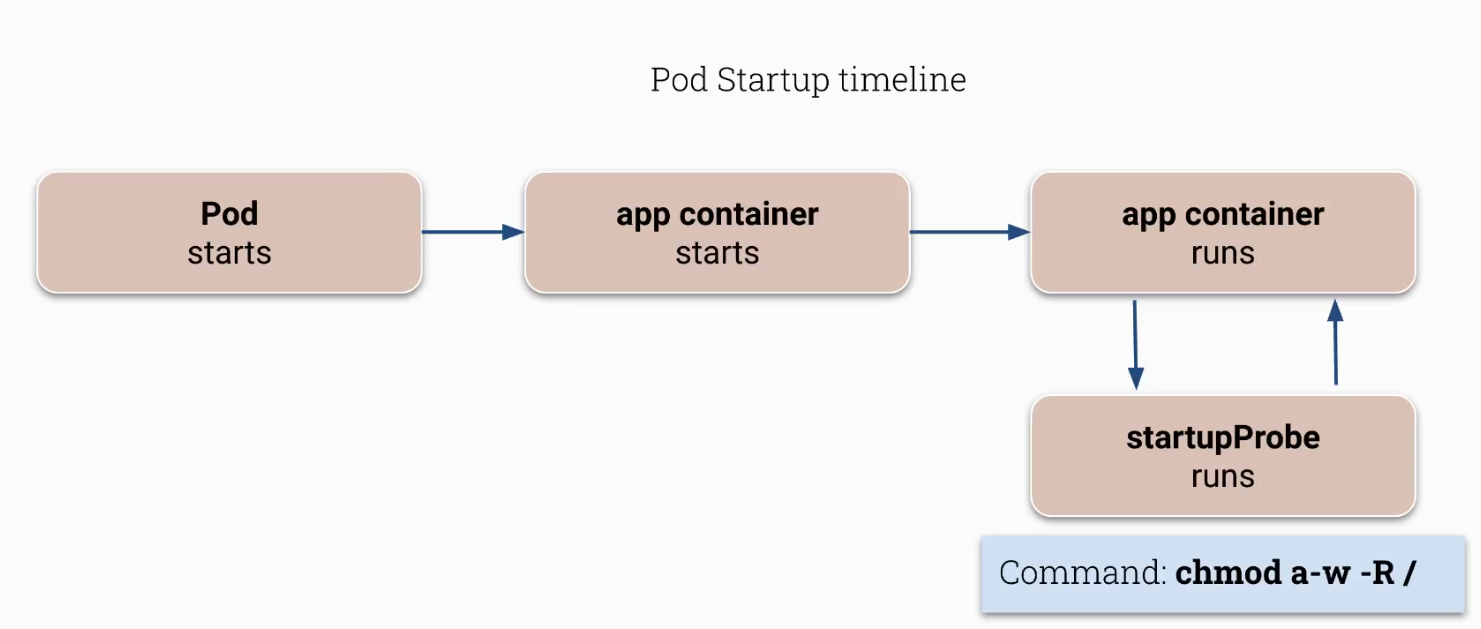
Interesting example of how startupProbe can be used to make a container a bit more secure
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
root@cks-master:~# cat immutable.yaml
apiVersion: v1
kind: Pod
metadata:
creationTimestamp: null
labels:
run: immutable
name: immutable
spec:
containers:
- image: httpd
name: immutable
resources: {}
startupProbe:
exec:
command:
- rm
- /bin/bash
initialDelaySeconds: 1
periodSeconds: 5
dnsPolicy: ClusterFirst
restartPolicy: Always
status: {}
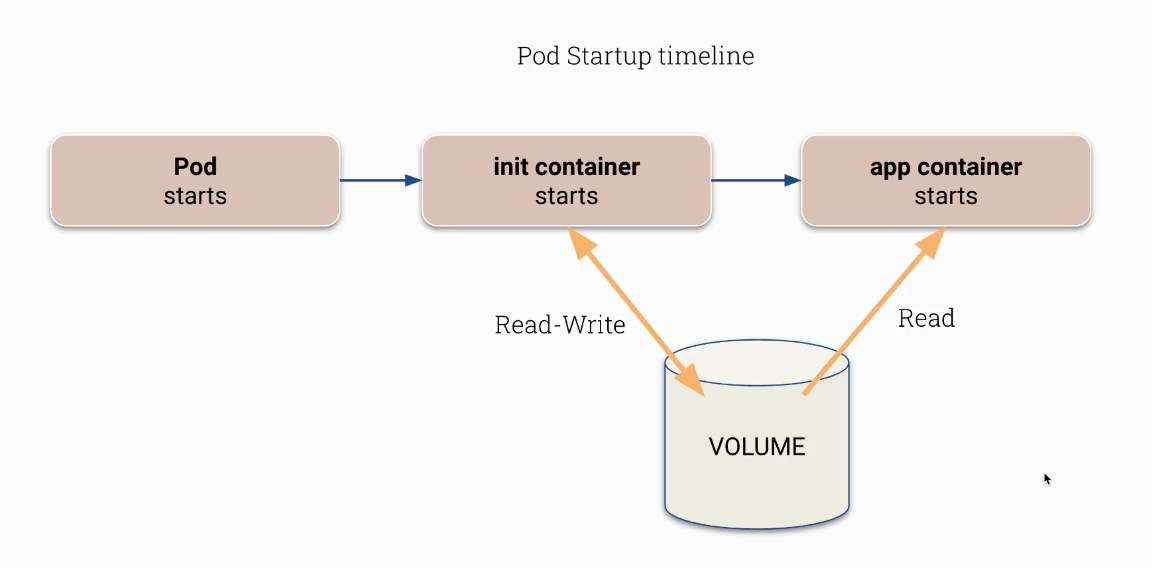
ReadOnlyRootFilesystem example
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
cat immutable.yaml
apiVersion: v1
kind: Pod
metadata:
creationTimestamp: null
labels:
run: immutable
name: immutable
spec:
containers:
- image: httpd
name: immutable
securityContext:
readOnlyRootFilesystem: true
volumeMounts:
- name: pid
mountPath: "/usr/local/apache2/logs/"
volumes:
- name: pid
emptyDir: {}
dnsPolicy: ClusterFirst
restartPolicy: Always
status: {}
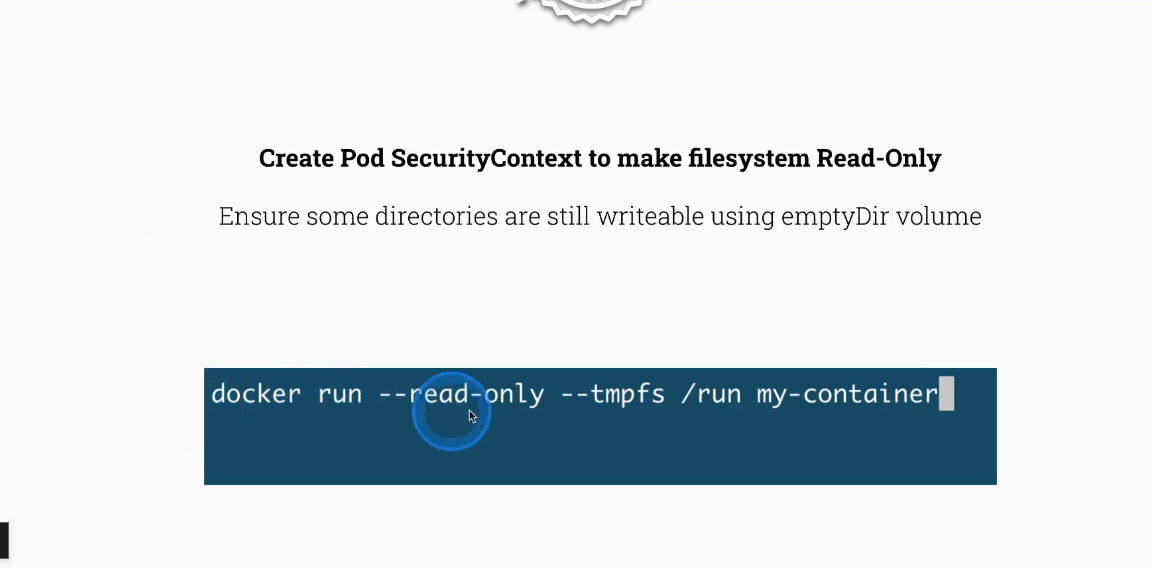
If you come from Docker world
Task
Generate a pod recipe with a read-only root filesystem. This command creates a dry-run YAML manifest for a busybox pod that sleeps for one day.
1
k run pod-ro -n sun --image=busybox:1.32.0 --dry-run=client -oyaml --command -- sh -c 'sleep 1d' > pod.yaml
Then add the readOnlyRootFilesystem security context to the generated manifest.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
controlplane $ cat pod.yaml
apiVersion: v1
kind: Pod
metadata:
creationTimestamp: null
labels:
run: pod-ro
name: pod-ro
namespace: sun
spec:
containers:
- command:
- sh
- -c
- sleep 1d
image: busybox:1.32.0
name: pod-ro
resources: {}
securityContext:
readOnlyRootFilesystem: true
dnsPolicy: ClusterFirst
restartPolicy: Always
status: {}
This post is licensed under CC BY 4.0 by the author.